Beyond Marketing Promises
Cybersecurity experts evaluate VPNs differently than casual users. Instead of focusing on slogans, they examine technical credibility. A professional VPN推薦 is based on evidence, transparency, and verifiable security practices.
VPN推薦 criteria reflect this expert-driven approach.
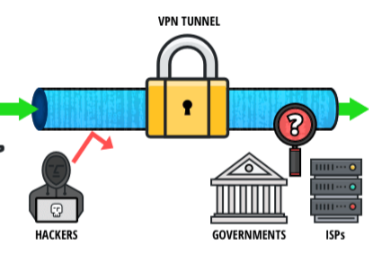
Encryption and Protocol Integrity
Experts prioritize strong, modern encryption and well-maintained protocols. Weak or outdated standards are immediate red flags. A serious VPN recommendation includes providers that regularly update their security stack.
VPN推薦 assessments consistently rank protocol quality as a top factor.
Logging Policies and Audits
No-logs claims mean little without verification. Cybersecurity professionals look for independent audits and clear documentation. VPN推薦 frameworks heavily favor providers with proven transparency.
Infrastructure and Jurisdiction
Server ownership, data center security, and legal jurisdiction all influence trustworthiness. A reliable VPN recommendation considers where servers are located and which laws apply. VPN推薦 analysis treats jurisdiction as a core security element.
Expert-Level Trust
For professionals, reliability is about consistency and accountability. A credible VPN recommendation aligns with expert expectations. VPN推薦 bridges the gap between technical rigor and user-friendly security.